Image by Kent Buckley
Prior to two weeks ago, when this reporter alerted authorities that they had exposed critical data, anyone online was able to freely access a City of Boston automated license plate reader (ALPR) system and to download dozens of sensitive files, including hundreds of thousands of motor vehicle records dating back to 2012. If someone saw your shiny car and wanted to rob your equally nice house, for example, they could use your parking permit number to obtain your address. All they had to do was find the server’s URL.
The open online server was a file share, primarily used for municipal parking enforcement to transfer and store vehicular permit information and nearly one million license plate numbers. This was all waiting to be discovered by anyone spelunking Google for terms including “Genetec,” the name of a Canadian surveillance company that owns the popular AutoVu brand of license plate readers.

Boston was among the first cities to deploy ALPRs and began beta-testing such devices more than 10 years ago. AutoVu had just obtained multiple patents for the technology, and the Boston Transportation Department (BTD) outfitted vans with pairs of cylindrical cameras alongside bright sodium lights and with them commenced extremely conspicuous surveillance of parked cars. ALPRs were eventually noticed by watchdogs, and in 2004 spurred a public records request, which was denied by the BTD on the grounds that the database was privately owned and “on loan” from AutoVu.
That was more than 10 years ago, and the pitfalls of using third-party outfits for these kinds of operations appear to have become more treacherous. Back then, few people were talking about the liability of having private companies store privileged and potentially compromising metadata. But even though the vulnerability of these systems has since been noted by privacy rights groups, cities all around the world still trust businesses like Genetec. A global provider of state-of-the-art surveillance and security products, the company began its acquisition of AutoVu in 2005, and to this day still sells government spy gear under the legacy brand name.
While Xerox and Genetec executives contribute to several pols on Beacon Hill, including Gov Charlie Baker, most of their Massachusetts money is made at the municipal level. Boston, for one, has been a trusty Genetec customer—in 2013, the surveillance behemoth even furnished free “testing” software licenses, which are otherwise valued at thousands of dollars, for a facial recognition program carried out over the first two Boston Calling concerts. Unbeknownst to attendees, all concertgoers were recorded and categorized according to searchable info based on criteria ranging from their race and height to the time and place they were taped.
On the ALPR front, Genetec shirks all responsibility for the aforementioned open portal, even though a remote desktop client terminal, which was also left exposed, shows they had direct access. Reached by email for this story, the company’s Vice President of Marketing and Product Management Andrew Elvish wrote that the server in question was a “location used by a customer to transfer data to be used in a parking or law enforcement patrol car, equipped with a Genetec system.” The data, Elvish added, was “not gathered by a Genetec AutoVu ALPR system … [which is] automatically encrypted.”
Digging deeper, further investigation of the IP address where the ALPR system was located revealed that Affiliated Computer Services (ACS), a Xerox subsidiary, owns the server. This reporter contacted Xerox upon making this discovery, and within two hours, the portal was removed from public view.
The following week, a Xerox spokesperson responded to an inquiry about the Boston matter in an email, claiming that, after an initial review, the company determined that the contents of the server included “publicly available information used to enforce residential parking regulations such as license plate numbers.” In any case, a 1994 federal law, the Driver’s Privacy Protection Act, is supposed to prevent non-governmental third parties from accessing a person’s name, home address, or telephone number through a motor vehicle database. For safety reasons, plate numbers are not personal information, but federal safeguards have for some reason not extended to Xerox, which sells “comprehensive name and address acquisition services” that toll and parking providers use to locate and ticket violators.

“[This is] just the most recent problem with Boston’s license plate tracking program management,” says Kade Crockford, director of the ACLU of Massachusetts Technology for Liberty Project. A regional authority on privacy and a harsh critic of ALPRs, Crockford was shocked by the magnitude of this apparent user error. Upon being alerted to the exposed data, one ACLU employee discovered his own plate number and address in the database, as did other Boston residents who park and drive around the city. Presented with that information, Xerox referred additional questions to the Boston Transportation Department. In turn, a BTD spokesperson wrote in an email that the agency is investigating the matter, and declined to offer any explanation for the server’s insecurity.
This is not the first time Hub authorities have been caught with their guard down on this matter. As journalist Shawn Musgrave, working with the public records news site Muckrock, reported in 2013, the Boston Police Department “inadvertently released to the [Boston Globe] the license plate numbers of more than 68,000 vehicles that had tripped alarms on automated license plate readers over a six-month period,” triggering “immediate doubts about whether the police could reliably protect the sensitive data.” Yet the coverup continues.
As members of the ACLU and others who track so-called smart surveillance in Boston recall, at a recent City Council hearing, BPD officials claimed that the police actually stopped using license plate readers because of concerns about privacy violations. (In 2013, the department announced that it was indefinitely suspending ALPR use.) Meanwhile, files in the BTD database that Xerox and the city left exposed logged several hundred daily emails to the BPD between early 2013 and last month, indicating that police are, as Crockford explains, “still engaged in the tracking of our license plates, albeit using data collected by the transportation department.”
In collecting data, the BTD patrols city blocks—in some cases, both literally and figuratively sweeping the street with ALPR-equipped sanitation trucks—and not exclusively in search of plates belonging to scofflaws. Files obtained in our investigation reveal that as the BTD’s software searches databases, it alerts department operators if a plate is connected to a “convicted person on supervised release,” or to someone pegged to a “protection order.” Commonly called hotlists, these compendiums are created by fusing criminal intelligence from sources like the FBI’s National Crime Information Center and the AMBER Alert program, as well as from data furnished by banks, collection agencies, and the civil court system.
It’s not clear whether or how the public is any safer when authorities use massive watchlists. In Boston, a city of approximately 600,000 people, parking enforcement has one hotlist with 720,000 hits, each of which notes a plate number, location info, and available make and model data. Among the targets listed in August: 19 license numbers classified as “immediate threats,” nearly 4,000 affiliated with “wanted persons,” 25 plates linked to bad checks, 75 tied to payment defaults, and 468,617 flagged for cancelled insurance. Also exposed were 2,500 hits on a “Gang/Terrorist Watch,” which Crockford says is “problematic from both public safety and civil liberties perspectives.”

Regardless of the claims made by officials, none of this prying is likely to end soon, as plate surveillance has become routine over time. The relationship between Boston and Xerox goes back decades, and a 2013 company case study even quotes former BTD Parking Clerk Director Gina Fiandaca praising the enterprise. “Xerox is always protective of the city, our data, and our integrity,” Fiandaca said. The same company research found that, through the convenience and accuracy of automated ticketing, Xerox helped create a “culture of compliance.”
If Boston’s deployment of ALPR, be it by the police, parking clerks, or Xerox as a proxy, seems reckless, it’s also not unique. Rather, it reflects a national law enforcement addiction to big data. The Electronic Frontier Foundation calls this warehousing of vehicle info a “public records act nightmare,” and warns that the risk of compromise or misuse grows as data is retained for long periods of time. In any place where authorities hold records indefinitely, mislead the public and reporters about retention, and fail entirely to secure data, said nightmares are bound to get darker before there is significant sunshine. Fortunately for the people of Massachusetts, Big Brother let its guard down this time, and was exposed.
If not for incompetence, we’d have no transparency at all.
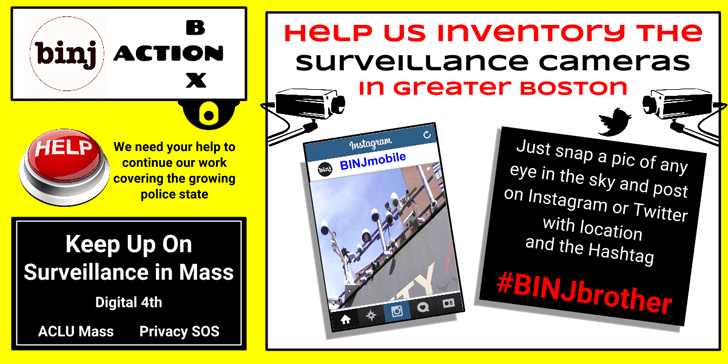
This article was produced in collaboration with the Boston Institute for Nonprofit Journalism. For more info on this and other projects, visit medium.com/@binj and follow on Twitter @BINJreports.